5 Critical Terraform Enhancements for Smarter Infrastructure Management
In the rapidly evolving world of infrastructure as code, HashiCorp Terraform continues to push boundaries. Over recent months, the engineering team has delivered a suite of updates that eliminate blind spots, bolster governance, and tighten security across the entire lifecycle. From granular cost analytics to project-level controls, these features empower platform teams to manage infrastructure with unprecedented precision. Here are five must-know additions that are transforming how organizations operate.
1. Billable Resource Analytics: Full Cost Visibility Now GA
Understanding where infrastructure costs come from has always been a challenge with Resources Under Management (RUM)-based billing. Previously, HCP Terraform customers could only see the total billable managed resources at the organization level. This left teams in the dark about which projects or workspaces were driving consumption, making it difficult to estimate future costs or identify waste.
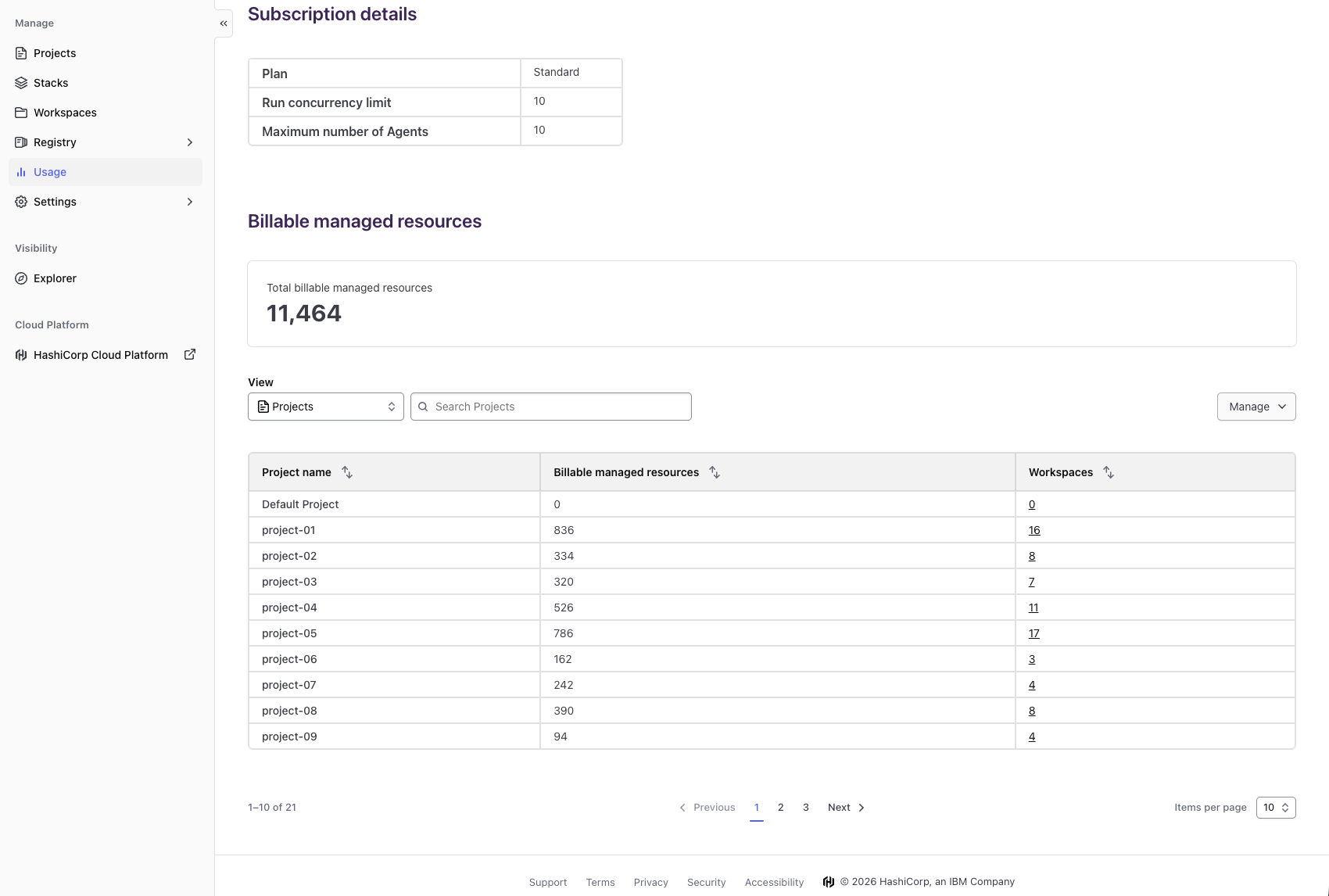
Now, with the general availability of billable resource analytics, organizations gain a self-service view that breaks down current totals by project and workspace. Decision makers can pinpoint high-consumption areas, reduce unnecessary spending, and optimize investments. This feature is accessible through the existing usage page on any paid HCP Terraform plan. The benefits are twofold: cost visibility and predictability let you manage spending proactively, while data-driven decision making enables strategic resource allocation aligned with business priorities. No more reacting to surprise bills—take immediate action on cost optimization.
2. Project-Level Remote State Sharing for Seamless Collaboration (GA)
Platform teams managing large-scale infrastructure often face a trade-off when sharing state data across workspaces. Without granular control, you either overshare sensitive information or create silos that hinder collaboration. The new project-level remote state sharing feature (now GA) resolves this by allowing administrators to define state sharing boundaries at the project level.
This means different teams can securely access state outputs from workspaces within their project without exposing data to unrelated projects. It reduces the governance burden while enabling efficient data flow between dependent systems. By eliminating the need for complex workarounds, teams can maintain security and accelerate development. This update is available in both HCP Terraform and Terraform Enterprise, giving organizations flexibility in how they structure their infrastructure ownership.
3. Module Testing with Dynamic Credentials for Enhanced Security (GA)
Testing Terraform modules is critical, but doing so with static credentials introduces risk. The general availability of module testing for dynamic credentials addresses this gap. It allows you to run tests that automatically generate temporary, scoped credentials, ensuring that test runs don’t leave permanent secrets exposed.
This feature integrates with HCP Terraform’s run environment, dynamically provisioning credentials just for the test execution. It not only improves security by following the principle of least privilege but also simplifies test setup. Development teams can now validate module behavior against real infrastructure without worrying about credential rotation or leakage. The dynamic approach means tests are more realistic and safer, fostering a culture of continuous integration and deployment with confidence.
4. Project-Level Notifications for Targeted Alerts (GA)
Historically, notification settings in Terraform worked at the workspace level or organization level, leaving a gap for project-wide alerts. The new project-level notification feature (now GA) fills this void, enabling you to configure notifications for all workspaces within a project at once.
This is a game-changer for platform teams who manage dozens of workspaces under a single project. Instead of setting up the same notification endpoint (e.g., Slack channel, email, or webhook) for each workspace individually, you define it once at the project level. Any run events—successes, failures, or planning stages—trigger alerts across the entire project. This reduces administrative overhead and ensures no workspace is missed. It also allows project owners to standardize alerting policies, improving incident response times and operational consistency.
5. Registry Tagging for Better Module Discovery (Beta)
As your module registry grows, finding the right module version becomes challenging. The registry tagging capability (currently in Beta) introduces a flexible way to categorize and filter modules using custom tags. Tags can represent version maturity (e.g., “stable”, “deprecated”), compliance requirements, or team ownership.
This feature lives in the Terraform Registry interface, allowing you to assign multiple tags per module or version. Users can then search and filter by these tags, dramatically reducing the time spent hunting for appropriate modules. For large organizations with diverse module catalogs, tagging improves discoverability and encourages reuse. It also enables governance by letting teams mark modules that are approved for production. During Beta, feedback is welcome to refine the tagging schema and integration with existing workflows.
Conclusion
These five updates collectively represent a leap forward in making Terraform more transparent, secure, and collaborative. From the granular cost insights of billable resource analytics to the efficiency of project-level notifications, each feature addresses a real pain point for modern infrastructure teams. Whether you’re a platform engineer managing resource consumption or a developer seeking safer module testing, these enhancements deliver immediate value. As HashiCorp continues to iterate, staying current with these capabilities ensures your organization remains at the forefront of infrastructure management. Check out the billable resource analytics and other features to start optimizing your Terraform workflows today.
Related Articles
- Testing Sealed Bootable Container Images for Fedora Atomic Desktops
- Upgrading to Fedora Workstation 44: A Complete Guide
- Your Complete Guide to Installing or Upgrading to Fedora Linux 44
- KDE Secures €1.28 Million Boost from Sovereign Tech Fund for Plasma and KDE Linux Development
- Canonical Unveils Ubuntu 26.04 LTS 'Resolute Raccoon' with Wayland-Only, GNOME 50, and Linux 7.0 Kernel
- Critical Linux Kernel Flaw 'Copy.Fail' Enables Unrestricted Root Access Across Major Distributions
- 10 Game-Changing Performance Wins in Linux 7.1-rc1 for AMD Ryzen Threadripper
- Meta Slashes 8,000 Jobs as Zuckerberg Blames AI Arms Race and Infrastructure Costs